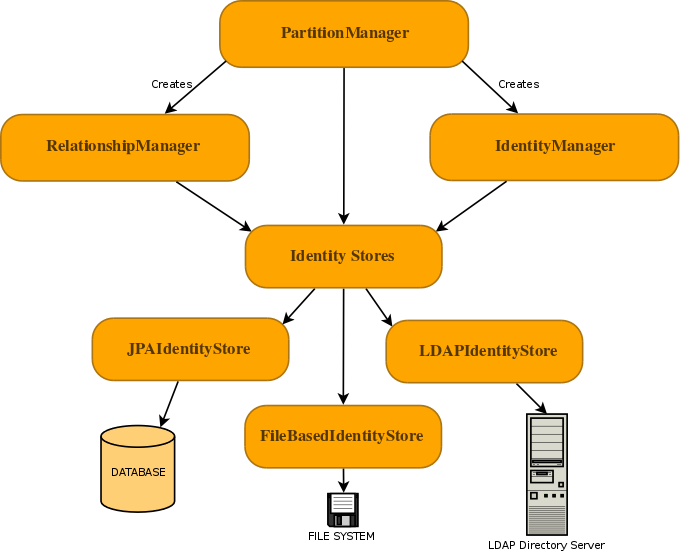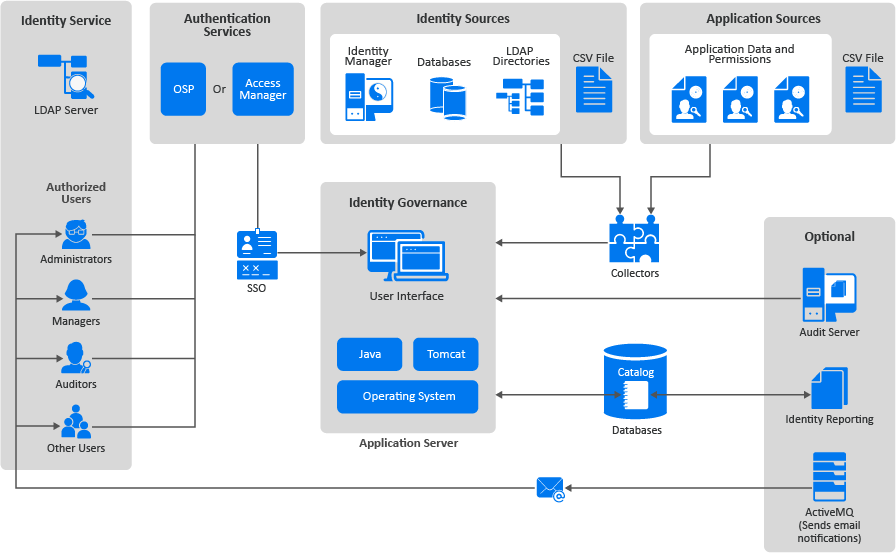
Understanding the Identity Governance Components - Identity Governance 3.6 Installation and Configuration Guide
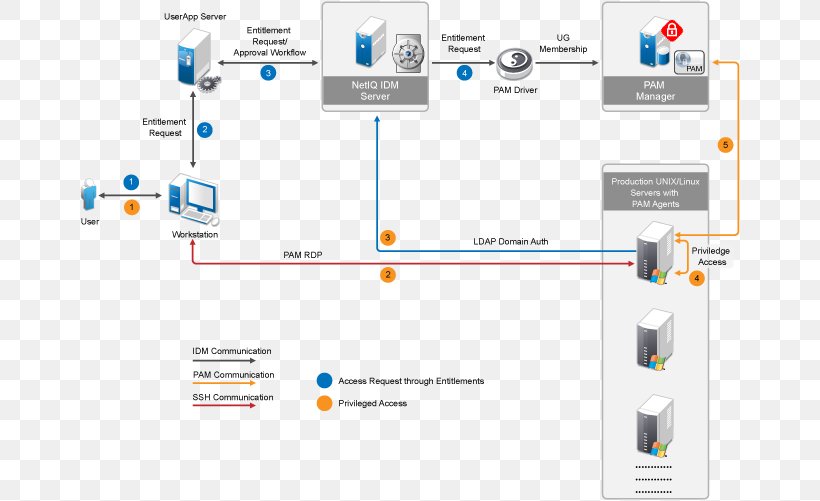
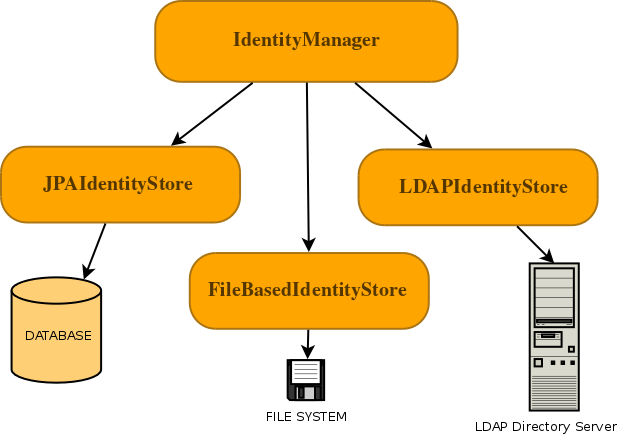
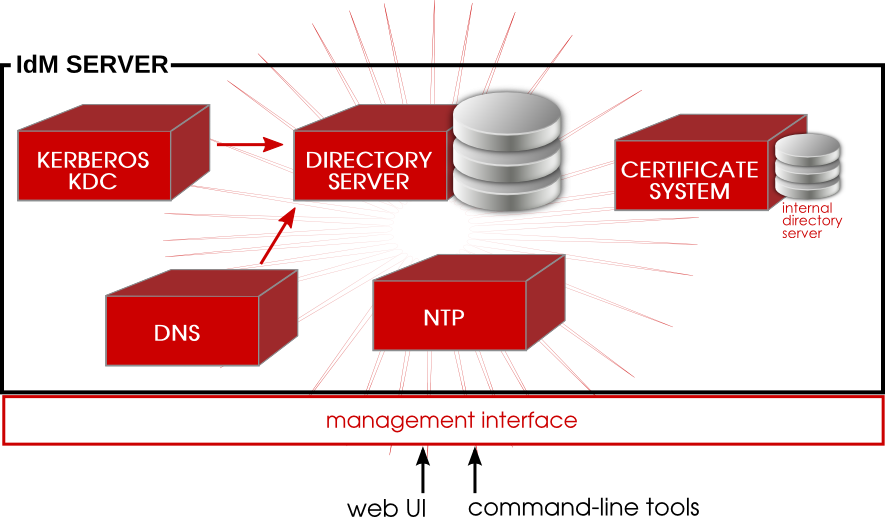
NetIQ Identity Manager Identity Management Technology Lightweight Directory Access Protocol, PNG, 661x501px, Netiq, Access Control, Brand,

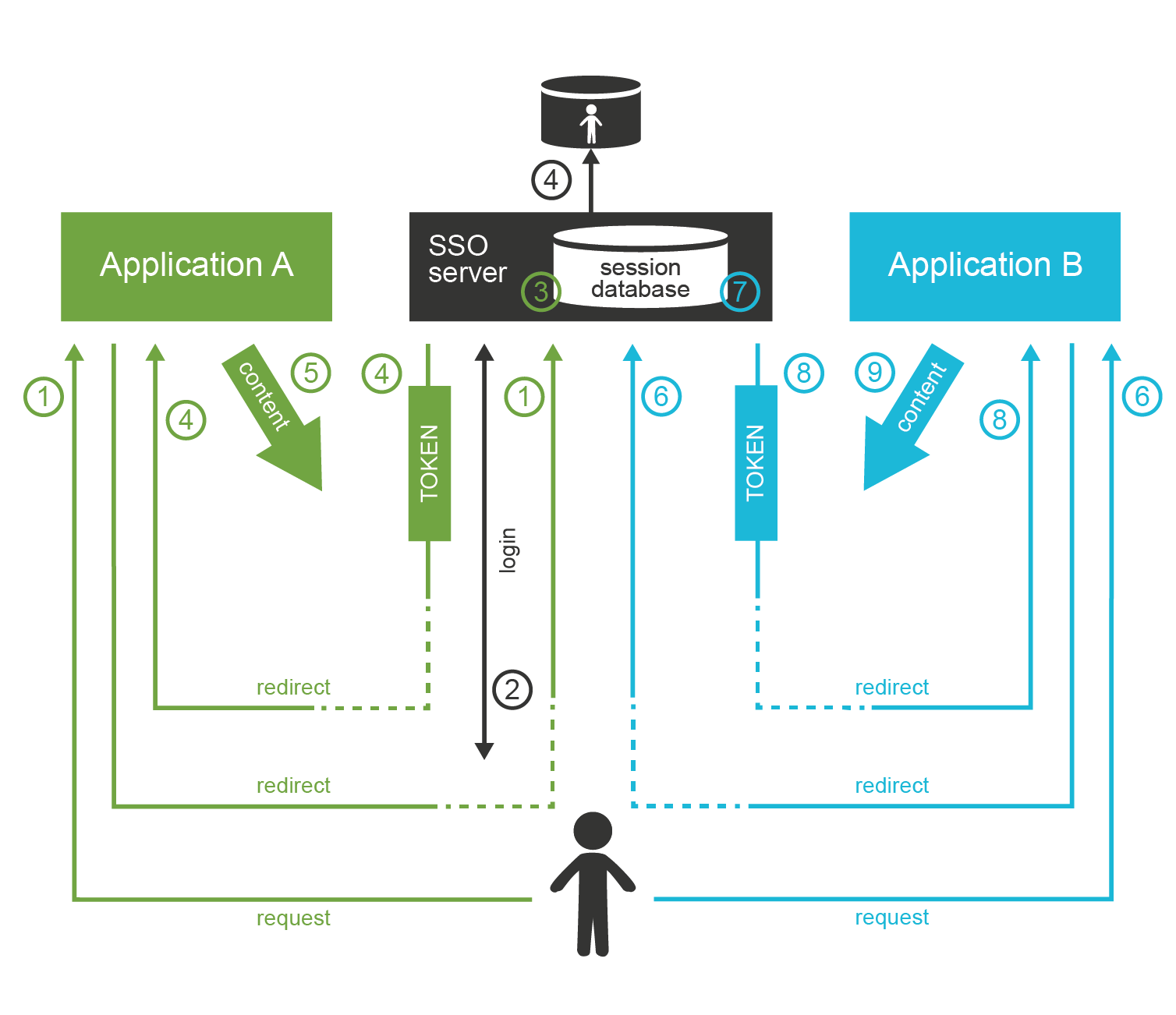
Forefront Identity Management – Certificate Management (FIM CM 2010) – Part 2 | Ammar Hasayen - Blog