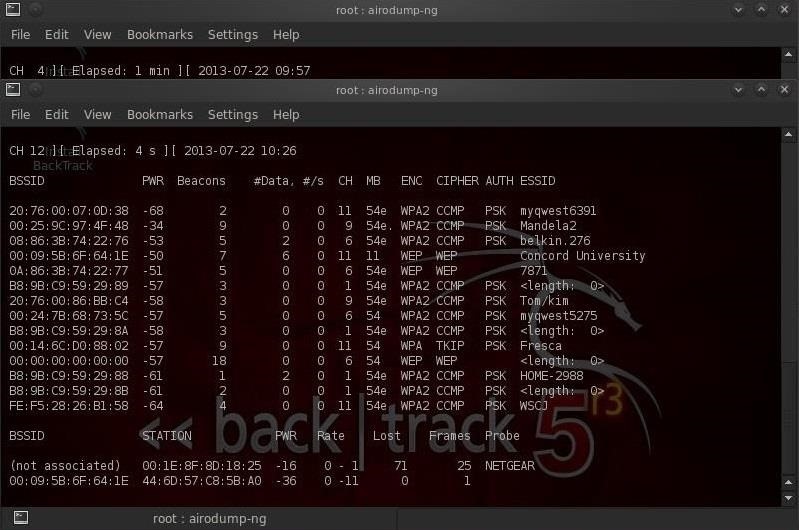
How to Hack Wi-Fi: Performing a Denial of Service (DoS) Attack on a Wireless Access Point « Null Byte :: WonderHowTo

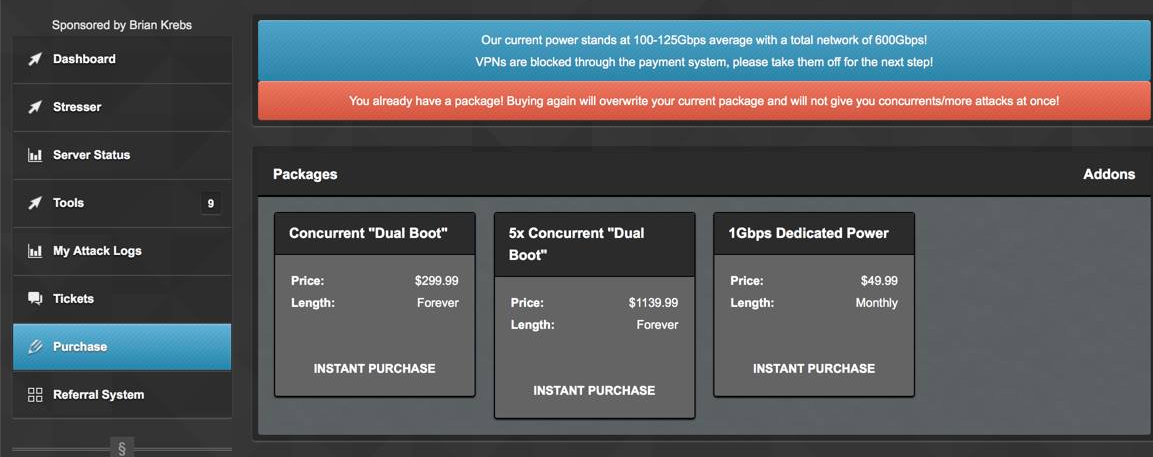
How to Brute-Force Drupal6 login pages? (DDoS, Backtrack 5 r3, Cyber Security, Metasploit) by Hakin9Magazine - Issuu
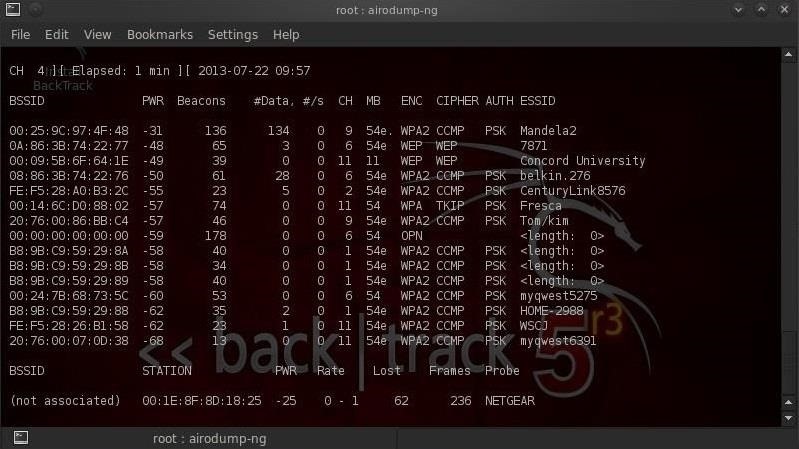
How to Hack Wi-Fi: Performing a Denial of Service (DoS) Attack on a Wireless Access Point « Null Byte :: WonderHowTo

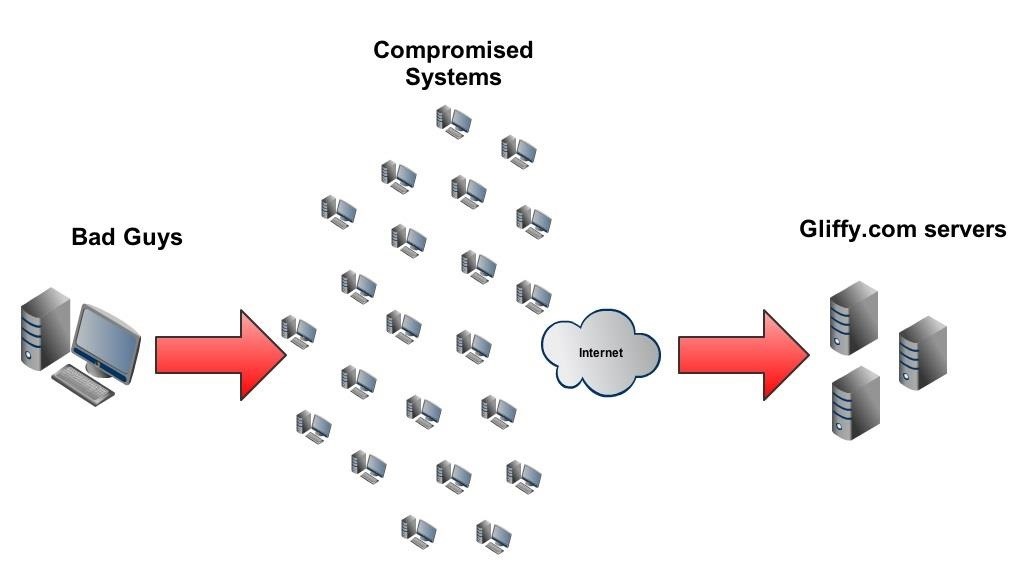
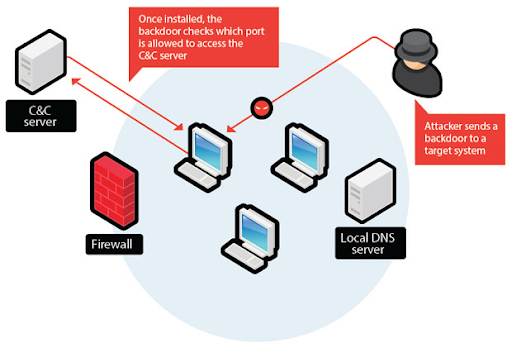
Meet Remaiten : Malware Builds Botnet on Linux based routers and potentially other (IoT) devices | PPT

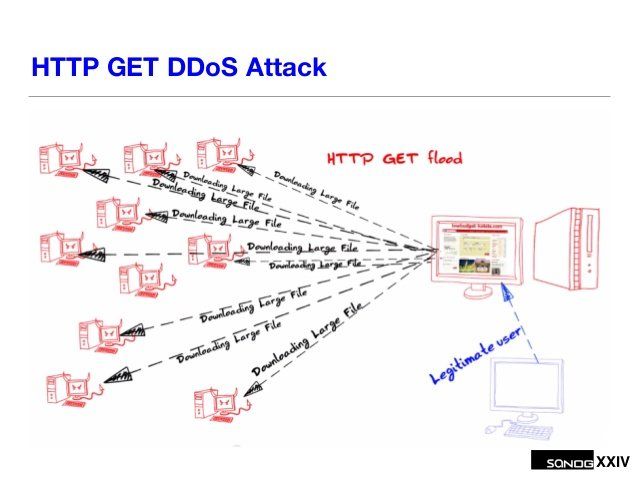
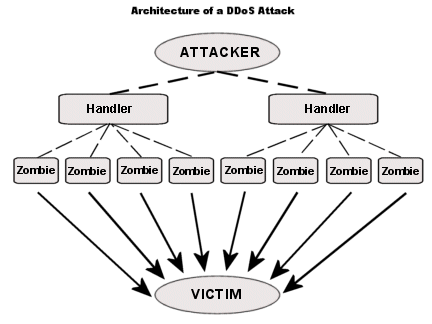
Future Internet | Free Full-Text | Effective and Efficient DDoS Attack Detection Using Deep Learning Algorithm, Multi-Layer Perceptron
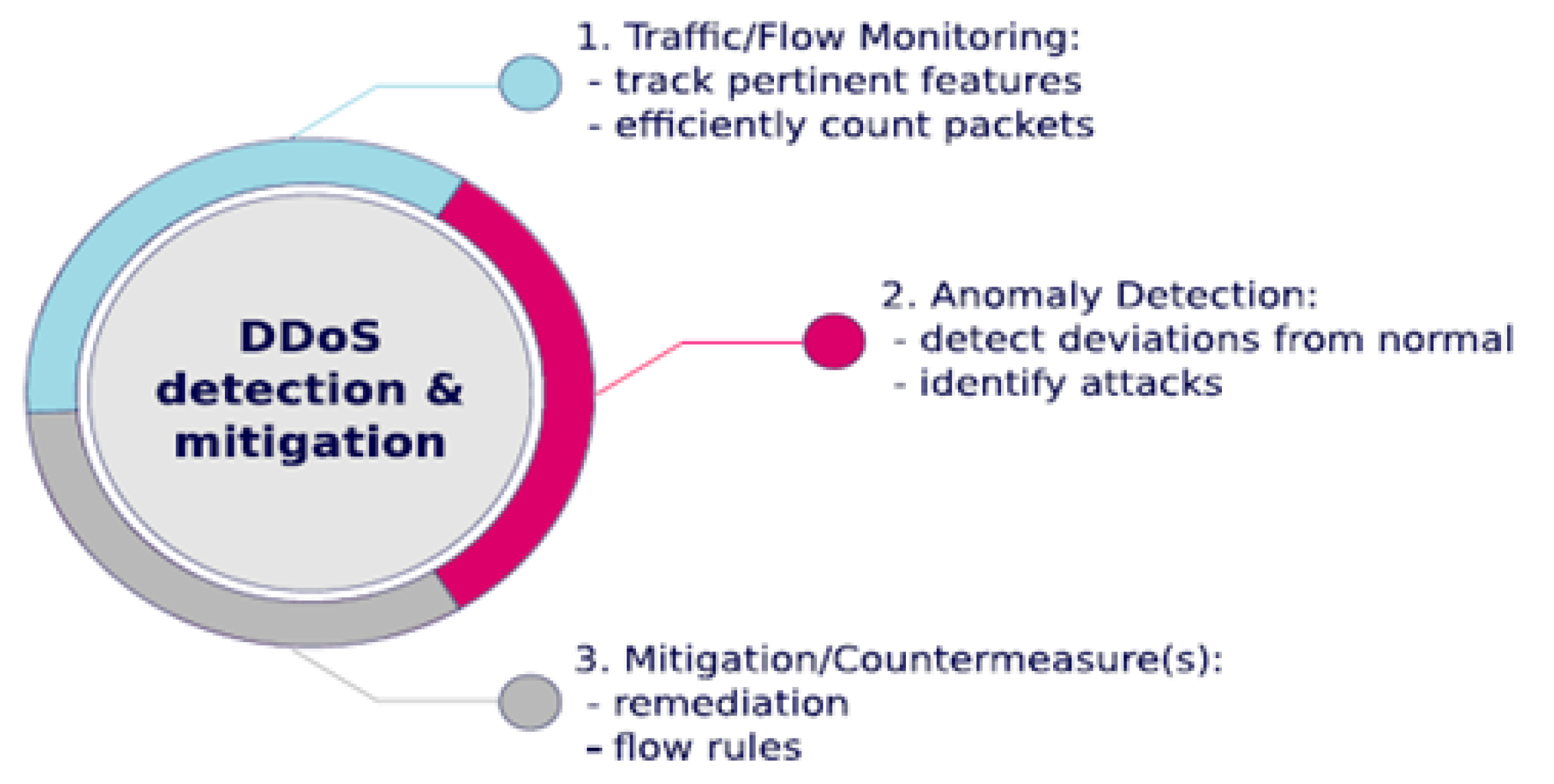
Future Internet | Free Full-Text | Effective and Efficient DDoS Attack Detection Using Deep Learning Algorithm, Multi-Layer Perceptron